Students wonder out loud when they’ll actually need algebra after high school. Districts have started to change their high school math curriculum to focus on actual problems first because most students can do the work, but they can’t find a reason to care. The idea is to show students why it matters before asking them to memorize formulas.
Most math classes look the same as they did twenty years ago. A teacher writes on the board, explains a concept, shows the formula, works through examples, and then assigns twenty problems for homework. Students write everything down, finish the assignment, take a test, and forget most of it.
The same pattern happens semester after semester because math feels like something to survive instead of something useful.
Put Real Problems First
Word problems about two trains leaving different stations are ridiculous. Nobody solves that in actual life. What gets attention is a problem connected to something students might genuinely face.
Programs like Illustrative Mathematics and Open Up Resources build entire units around authentic scenarios where students need math to answer real questions.
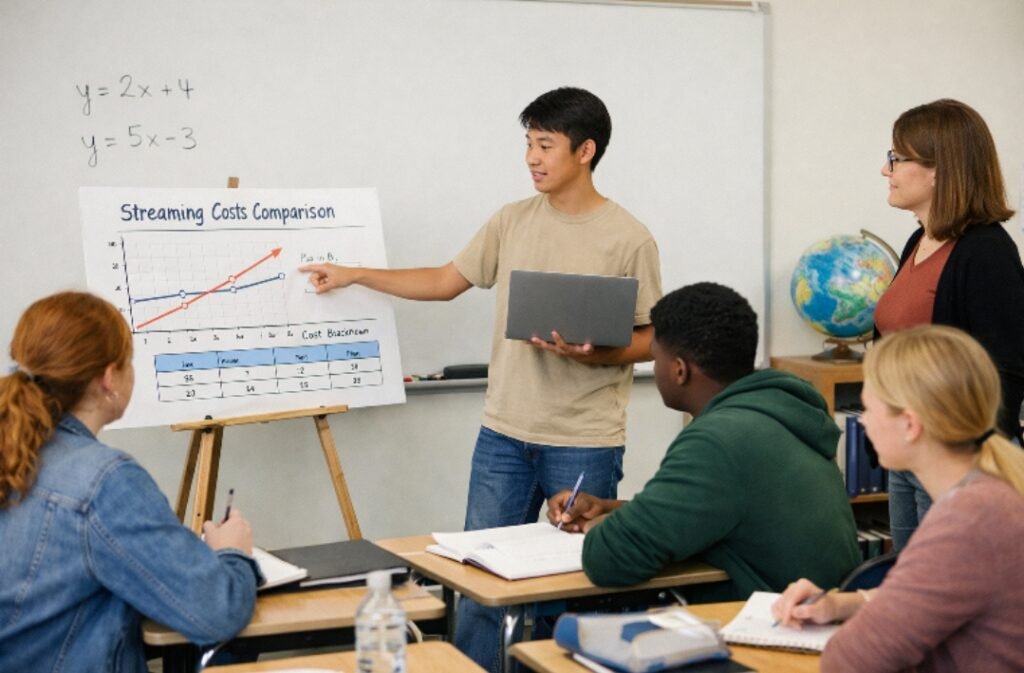
When a teacher opens a lesson by asking students to figure out which streaming service costs less based on how much they watch, students lean in.
They try to solve it with math they know, get stuck, then discover a linear equation gives them what they were looking for. The formula stops being an abstract rule and becomes a useful tool.
Make Invisible Ideas Visible
Graph paper and calculators have been around forever, but digital tools do something those can’t. Desmos lets students type an equation and see the curve show up right away. Change one number and the whole graph moves. Students can see what happens instantly instead of plotting twenty points by hand.
GeoGebra works the same way for geometry. Students build a triangle on screen, measure the angles, then drag the corners around. The software updates all the measurements as they move things. Students watch the numbers change, but they notice the angles always add up to 180 degrees.
When technology becomes part of regular lessons, 76% of students say it makes learning more engaging.
Turn Repetition into Something Students Want
Students need practice to get good at math. Worksheets don’t work, though, because rows of similar problems just annoy people.
Khan Academy and Delta Math turn practice into progression where students work through problems at their own pace and see exactly where they stand. IXL and Mathspace add game elements where students earn points and compete with classmates.
Digital platforms catch mistakes right away and show hints on the spot. Students fix their thinking before it becomes a habit.
Show Students Who Use It
Telling teenagers that math is important doesn’t work. What actually works is showing them a specific person doing a specific job that needs the exact concept from class. An architect explaining how she calculates roof angles with trigonometry beats any lecture about why math matters.
Videos from sources like Mathalicious or watching TED talks by mathematicians help. Guest speakers help more. When a student who loves basketball finds out that sports analysts use statistics to predict how players will perform, suddenly there’s a reason to pay attention.
Jobs that need strong math skills are growing fast, with STEM employment projected to grow at 10.8% through 2031 compared to just 5.3% for overall employment.
Give Students Multiple Ways to Show What They Know
Not every student does their best work on timed tests. Some understand concepts deeply but panic under pressure. Teachers who let students demonstrate mastery in different ways get a much clearer picture of who actually understands what.
Tools like Flipgrid let students explain their thinking out loud, while Padlet allows them to show work visually.
A statistics unit could end with a project instead of an exam. Students pick a dataset about something they care about, run the analysis using Google Sheets or Excel, make charts that explain what they found, and then present it to the class.
A geometry unit could have students design a building using SketchUp that meets requirements and defend every measurement with math. Those assessments show a real understanding that multiple-choice tests miss.
Let Students Struggle Before Stepping In
Teachers naturally want to help when students get stuck. That instinct ruins the learning process, though. Students need time to be confused. They need to mess up and try methods that go nowhere. Teachers who wait before helping end up with students who solve problems on their own instead of copying steps from the board.
A classroom where getting things wrong feels normal makes this possible. The teacher asks questions that help the student spot the error. The whole class talks about why that approach seemed smart and where it fell apart.
Other students throw out different ideas. The first student tries again and figures it out. It takes longer than just telling them the answer, but they actually remember it.
Conclusion
Math class works when students see a problem they actually want to solve before anyone shows them the formula. Digital tools make abstract ideas visible and concrete.
Real examples from actual jobs explain why any of it matters beyond getting a grade. Different ways to assess let students show what they know in whatever way works for them. What matters most is giving students time to work through confusion on their own instead of jumping in to save them right away.